
With increasing cyber security threats, it is vital for organisations to have wider visibility over their network. Cybercriminals today are targeting Active Directories (AD), performing reconnaissance to discover users, servers and computers in an enterprise network. They then move laterally to carry out multi-stage attacks, gaining access to abus organisational resources and data.
To gain more insights into potential threats, and to stop them before they attack, system administrators have to keep an eye out over the system generated logs.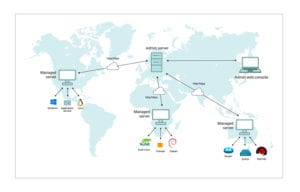
Different log generating aspects within the infrastructure are:
- Perimeter devices such as routers, switches, firewalls, and IDS/IPS.
- Servers.
- Applications that a business runs – such as databases, web servers, etc.
EventLog Analyzer helps in end-to-end log management, with agent and agentless methods of log collection, custom log parsing, complete log analysis (with reports and alerts), a powerful log search engine, and flexible log archiving options.
It centrally collects, normalises, analyses, correlates and archives log data from sources across the network. This component can process log data from 700+ sources including applications such as IIS/Apache web servers, Oracle, MS SQL, vulnerability scanners, and more. In fact, this component can process your in-house or custom application logs with its Universal Log Parsing and Indexing (ULPI) technology.
This component provides:
- Real-time email or SMS notification to help mitigate security attacks instantly.
- Out-of-the-box reports that help gain complete visibility into security frameworks.
- Powerful yet easy to use search engine that helps conduct root cause analysis or forensic investigations.
Curious how it works? Download a 30-day trial now with all features enabled!
This will give you the opportunity to test this solution out in your environment, so you can make sure everything works the way you want it to.
For any queries, pricing or if you get stuck with your trial, email us at sales@manageengine.co.nz
Dhruv Patel | Senior Pre-sales Solutions Engineer

