You may not have heard the term but you would have definitely come across these emails before. CERT NZ defines Business Email Compromise (BEC) as when an attacker gets access to an employee’s email account without their permission to carry out a range of attacks or scams. BEC can affect small companies through to large enterprises, and result in the loss of finances, private information and damage to the companies’ reputation.
It is a simple but increasingly costly scam. BEC attackers use various social engineering techniques, typically impersonating CEOs and other executives to trick unwitting employees down the company’s hierarchy.
According to the FBI, there are 5 types of BEC scams:
- The Bogus Invoice Scheme – Companies with foreign suppliers are often targeted with this tactic, wherein attackers pretend to be the suppliers requesting fund transfers for payments to an account owned by fraudsters.
- CEO Fraud – Attackers pose as the company CEO or any executive and send an email to employees in finance, requesting them to transfer money to the account they control.
- Account Compromise – An executive or employee’s email account is hacked and used to request invoice payments to vendors listed in their email contacts. Payments are then sent to fraudulent bank accounts.
- Attorney Impersonation – Attackers pretend to be a lawyer or someone from the law firm supposedly in charge of crucial and confidential matters. Normally, such bogus requests are done through email or phone, and during the end of the business day.
- Data Theft – Employees under HR and accounts are targeted to obtain personally identifiable information (PII) or tax statements of employees and executives. Such data can be used for future attacks.
BEC has been around for a number of years but scammers are constantly developing new ways to take advantage of their victims.
One example I’ve encountered recently involves an attacker spoofing the email address of a sales manager, who then emailed the account managers asking them to urgently purchase iTunes Gift Cards and send the gift codes back to him. The spoofed email also mentioned the sales manager was stuck in a meeting so could not answer any phone calls, in an attempt to stop the account managers from calling and confirming the instructions.
The account managers, out on the road, would read the email on their iPhones and wouldn’t know the email was spoofed. The iOS Mail app doesn’t show the sender’s email address until you select it. This scam is also known as the ‘Gift Card Scam’ Luckily in this case, the scam was not successful as all the account managers realised the email was not genuine and deleted it, or they contacted the sales manager to clarify the instructions. Demonstrating how important staff education and awareness is against even the most well engineered scams.
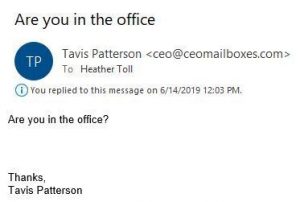
How a Gift Card Scam usually starts. Note the fake sender address.
Tips to prevent BEC
- Educate employees. While employees are a company’s biggest asset, they’re also usually its weakest link when it comes to security. Train staff to develop good security habits and be wary of suspicious emails. Confirm with a text or call to the person or business who sent you the invoice/request. As per my previous example, the spoofed emails got through the company’s security but staff awareness prevented any damage.
- Add an extra layer of security to accounts with two-factor authentication (2FA) or multi-factor authentication (MFA).
- Enforce a strong password policy, using strong, long and unique passwords on all accounts. A Password Manager can be used to help staff generate and manage their passwords.
Trend Micro has created a phishing awareness tool called Phish Insight. Their phishing simulator makes it easy for IT professionals to increase awareness and to train employees. The simulator is free to use, requires no installation and is incredibly realistic. Learn more here about Trend Micro Phish Insight and see how you can utilise it to increase phishing and security awareness.
Trend Micro Email Security also offers an affordable solution that integrates into the Trend Micro Smart Protection network, and uses artificial intelligence (AI) and machine learning to prevent BEC and other attacks. It is available as a standalone solution or as part of the Trend Micro Worry-Free Security Services Advanced suite. This features Worry-Free Security Services for endpoint protection, Email Security Standard for email filtering and anti-spam, as well as Cloud App Security for Cloud platforms such as Office 365 and Dropbox.
Curious how to apply AI and machine learning to prevent BEC attacks? Email us at sales@sofsol.co.nz to learn more.
